- By Heather MacKenzie
- February 17, 2021
- Nozomi Networks
- Feature
Summary
To accelerate their digital transformation, Intelligent Transportation Systems (ITS) are becoming more connected and complex, which unfortunately opens the door to new cyber risks. To ensure operational availability during this transition, deep visibility into ITS networks is required. Let’s look at the challenges faced by the maritime sector, and how they can be eased with ITS cybersecurity best practices and use of the right technology.

The World Economic Forum cites cyberattacks on critical infrastructure, including transportation, as the world’s fifth highest risk in 2020.1 At the same time, transportation and logistics organizations are rapidly evolving to improve their service levels and efficiency.
To accelerate their digital transformation, Intelligent Transportation Systems (ITS) are becoming more connected and complex, which unfortunately opens the door to new cyber risks. To ensure operational availability during this transition, deep visibility into ITS networks is required.
Let’s look at the challenges faced by the maritime sector, and how they can be eased with ITS cybersecurity best practices and use of the right technology.
Maritime asset owners can reduce risk with improved cybersecurity
The maritime industry transports 90% of the world’s trade.2 Like other industries, it’s becoming increasingly automated and remotely monitored. Shippers want to optimize voyages and track the operational status of things like:
- Load condition of the vessel
- Fuel consumption
- Position and route
- Machinery performance
- System efficiencies
Rapid digitization is fueling the development of Maritime Autonomous Systems (MAS), where new generation ships can be remotely controlled from land.
On the other hand, the level of system visibility and cybersecurity maturity in this sector is relatively low. Many ships contain devices and even systems that are unknown to their operators. Crew are not typically trained to identify phishing emails or manage network access control.
While dramatic situations like a vessel capsizing3 due to hacking are not out of the realm of possibility, they are still unlikely. Crew constantly observe ship behavior and can often employ manual or safety systems to correct performance that is out of normal range.
Disruptive events that are more likely to occur include:
- Employees or suppliers unintentionally causing cyber incidents that threaten operational reliability or are expensive to remediate
- Cyber criminals disrupting a company’s shipping operations or altering documents to facilitate drug smuggling
- Threat actors stopping ship-to-shore functions, such as crane operations, and stopping the flow of goods
Driven by the need to reduce risk, comply with international shipping standards,4 and meet insurer requirements, shipping companies are investing in cyber resiliency. An important capability lies in identifying maritime assets and tracking their communications. Networks should be monitored for vulnerabilities, threats, and unusual behavior that could indicate a cyberattack.
Fortunately, real-time OT/IoT visibility technology can be used to improve both operational availability and cyber resiliency, helping ensure the safety of transportation system as they transform.
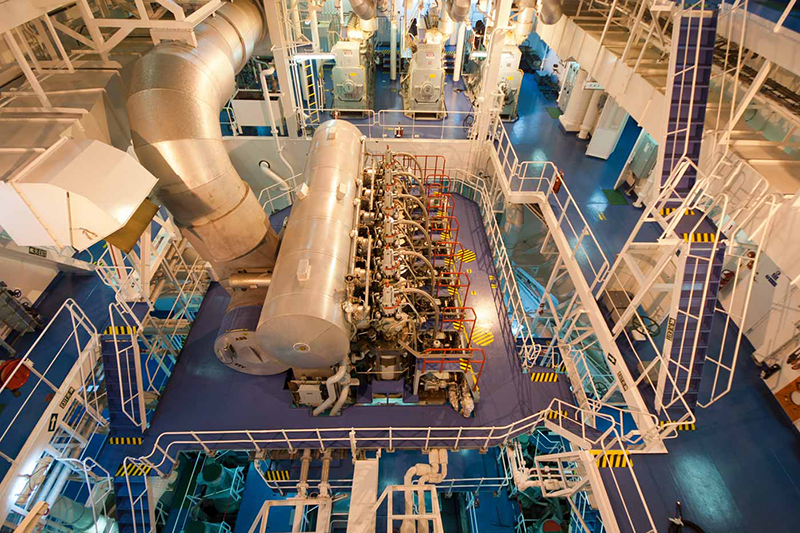 |
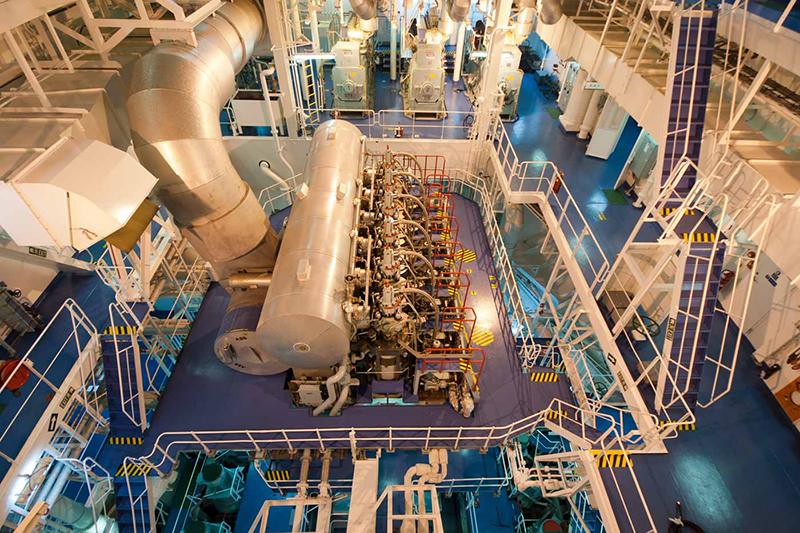
| The wide variety of controls and control systems on ships makes them challenging to monitor and secure. Nonetheless, ship owners are improving cybersecurity programs, in part because of international shipping standards. |
Improving network and operational visibility
The complex technology used within the maritime transportation environment makes consolidated OT/IoT visibility extremely difficult. It also expands the attack surface, increasing vulnerability to cyber threats.
To keep things running smoothly, security and operations teams need a simple way to inventory the wide variety of devices and systems used. The Nozomi Networks solution, for example, provides deep visibility across all control networks by automatically creating an accurate, centralized inventory of OT/IoT assets and keeping it up-to-date.
Our solution analyzes network traffic, using the data to build a live, interactive visualization of operational technology systems. An extensive amount of useful information is provided, including:
- A macro view of the entire ITS environment, with the ability to filter by subnets and network segments
- Detailed asset views that make it easy to drill down for deeper insight
- The role of each node and the traffic between nodes
- The protocols used to communicate between nodes and zones
- Network traffic information such as throughput, protocols and open TCP connections
- Detailed attributes of endpoints and connections
- Automated alerts that bring hardware, software and device changes to your attention
In fact, the breadth and depth of information often provides insight into previously unknown devices, connections and activity.
 |
|
Within minutes of deployment, the Nozomi Networks Solution provides comprehensive visibility into operational networks and ITS/IoT assets. It helps teams efficiently identify and mitigate cybersecurity and reliability risks. |
Deep visibility into transportation ITS networks builds operational resiliency
To stay on top of what’s happening on transportation system networks, OT/IoT visibility and threat detection is required. Security gaps related to people and processes can have a big impact on operational resiliency too. For example, the separation of IT and OT, combined with increasingly connected ITS control systems, can lead to blind spots and vulnerabilities. But with the right technology and a focus on best practices, transportation organizations can increase operational resiliency.
The Nozomi Networks solution is tailored to meet the unique requirements of transportation asset owners. Many of the world’s top transportation companies have chosen our innovative solution for OT and IoT visibility. It helps them accelerate digital transformation while reducing cyber risk. Find out how it can help you by downloading the document below or contacting us.
About The Author
Heather MacKenzie is the director of marketing communications with Nozomi Networks. Passionate about cybersecurity and communications, Heather has been writing about industrial security and networking since 2008. Her works helps OT/IT teams understand cyber and operational risks, and what they can do to improve resiliency. As Director of Marketing Communications, Heather leads a team responsible for Nozomi Networks branding, content and digital marketing.
Did you enjoy this great article?
Check out our free e-newsletters to read more great articles..
Subscribe

