- May 05, 2021
- Endress+Hauser, Inc.
- News
Summary
Cyberattacks targeting industrial plants can have grave consequences. And yet, many security concepts are either too complicated or too vulnerable. Cryptography experts at Endress+Hauser have developed the CPace standard, which uses simple passwords to provide a level of protection approaching that of certificate-based systems.

Digitalization promises greater productivity, efficiency and operational safety through connectivity between process engineering systems. Important components of industrial digitalization include field devices for measurement, control and regulation that are connected to the internet via technologies such as Bluetooth gateways. This connectivity has its price though, because it offers an attack surface to hackers and cybercriminals. If field instruments are tampered with, there is risk of a production standstill–or even plant damage and endangerment of people nearby.
Asymmetric cryptography
Cryptologists have developed asymmetric methods to avoid such situations. Rather than relying on just a single encryption key, these methods work with a pair of keys, one public and one private. Stored in digital certificates, these two keys must engage with one another before data can be exchanged. Yet when there are numerous small communication partners, which is often the case in industrial environments, this process soon becomes highly complex, requires extensive computing power and results in correspondingly high power consumption.
Password-based methods
Password-based protection systems are user-friendly in comparison, but are very prone to hacking with offline cyberattacks. Here, hackers first steal password-related information, for example by intercepting encrypted data during a login sequence. They then try out different passwords offline on their local computer until they find the correct one. The only way to prevent an attack like this from succeeding is by using sufficiently long encryption keys.
Invisibility cloaks and trapdoors
The CPace method developed by Endress+Hauser offers a happy medium. This method is easy to manage because it also functions with shorter, user-friendly passwords. It’s secure at the same time, since no password-related information is divulged during authentication between the field instrument and operations terminal. This "zero knowledge" approach relies on concealing data in background noise that works like an invisibility cloak. An attacker then has no option but to try out extremely long key sequences–and the chances for success dwindle to zero.
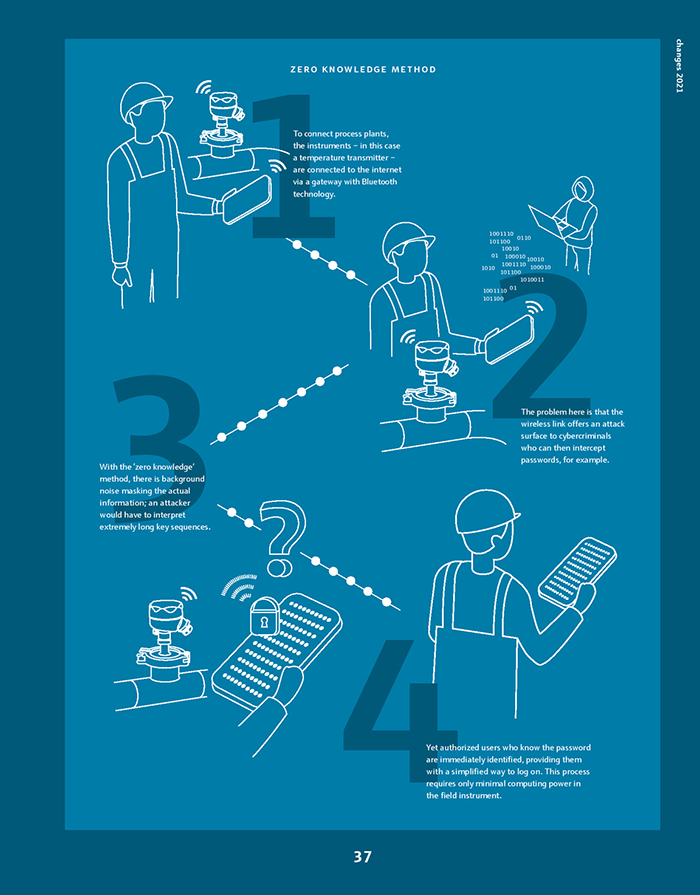
The CPace protocol differentiates between good and bad. Authorized users who know the password are immediately identified as such and directed through ‘trapdoors’ during authentication. These trapdoors are hidden shortcuts that significantly reduce computing time and power consumption. So the CPace method is particularly well suited for use in process engineering environments with hundreds or thousands of connected field instruments.
Approved by IETF
The CPace method has the potential to eventually protect internet-based applications well beyond the process industry. The CPace protocol has been recommended by the Internet Engineering Task Force (IETF), which oversees the standardization of internet communication protocols such as IP, TCP and HTTP.
Did you enjoy this great article?
Check out our free e-newsletters to read more great articles..
Subscribe

